Key Learnings from Files Present on the C2 Server of an Infamous Infostealer Malware
This method can be applied to multiple other C2 servers that we come across on a daily basis to check for any security misconfigurations…
Home » VirusTotal
This method can be applied to multiple other C2 servers that we come across on a daily basis to check for any security misconfigurations…
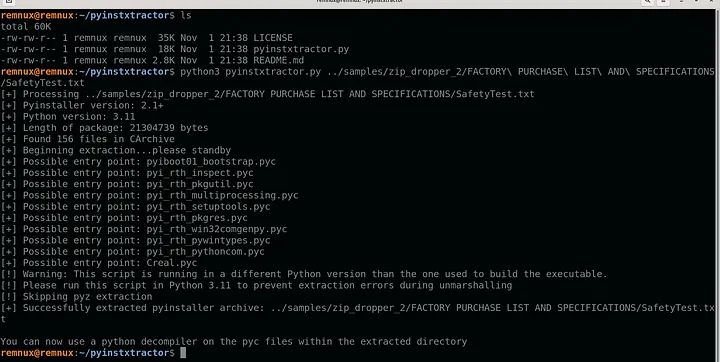
A ZIP/LNK payload and, with some luck, we will end up identifying the infostealer that is being dropped and its source code…

The background and the IOCs for this blog were gathered by an Expert helper on our forums and Malwarebytes researchers. Our thanks go out to

The cybersecurity landscape is rife with challenges, but some threats are quieter, subtler — and deadlier. Info stealers, the silent operators of the malware world,

In a recent campaign, North Korean threat actors have demonstrated a sophisticated approach by copying novel malware distribution techniques, notably those employed in the Clickfix
Stay informed with the latest insights in our Infostealers weekly report. Explore key findings, trends and data on info-stealing activities.